2 factor or multi-factor authentication (2fa for short) is a critical tool in maintaining your online security. Almost all web based services nowadays offer it, especially “high value” targets that may be used to steal your cash or identity like online banking, email, social media accounts and domain registrars.
The basic idea is that, when you login to your account from a new device, you not only have to enter your password but also a “one time code” generated by a separate device or piece of software, and delivered to you through a separate communication channel.
For example, you might have a keyring or token that allows you to press a button to receive a code, or an app on your phone that generates a new code every 60 seconds. In some cases, you will need to type in a code or click a link that has been sent to you via email, but far and away the MOST common form of 2fa uses SMS/TXT messages sent to your phone.
This is the most convenient way to set up and manage your 2fa (and in some cases it’s the only option offered by a lot of services) but there is one critical security flaw that goes along with it: SIM jacking.
What is SIM jacking?
SIM jacking is when someone fraudulently convinces your mobile phone company to transfer your number to another SIM card. In the case of an Australian prepaid mobile phone service, for example, your number can be transferred to another SIM card using only your date of birth and mobile number as verification. For postpaid phone services, all that’s required is a recent phone bill to verify proof of ownership.
While SIM jacking is more labour intensive and difficult to carry out than many other forms of attack such as guessing passwords and so on, it’s not hard to see how one of those “lower friction” exploits can be escalated to allow SIM jacking, and given the value available online now it’s not hard to see why SIM jacking attacks are on the rise globally.
How to protect yourself from SIM Jacking
There are a couple of ways you can help prevent SIM jacking. Firstly, take the protection of your personal information seriously. Don’t publish your birthday on social media, shred your mail or request digital delivery of bills and store them securely, enable 2fa via an app or hardware token where possible.
However, some critical services will only allow you to authenticate via SMS 2fa, and while you can personally take precautions, it’s more difficult to ask your staff to do the same.
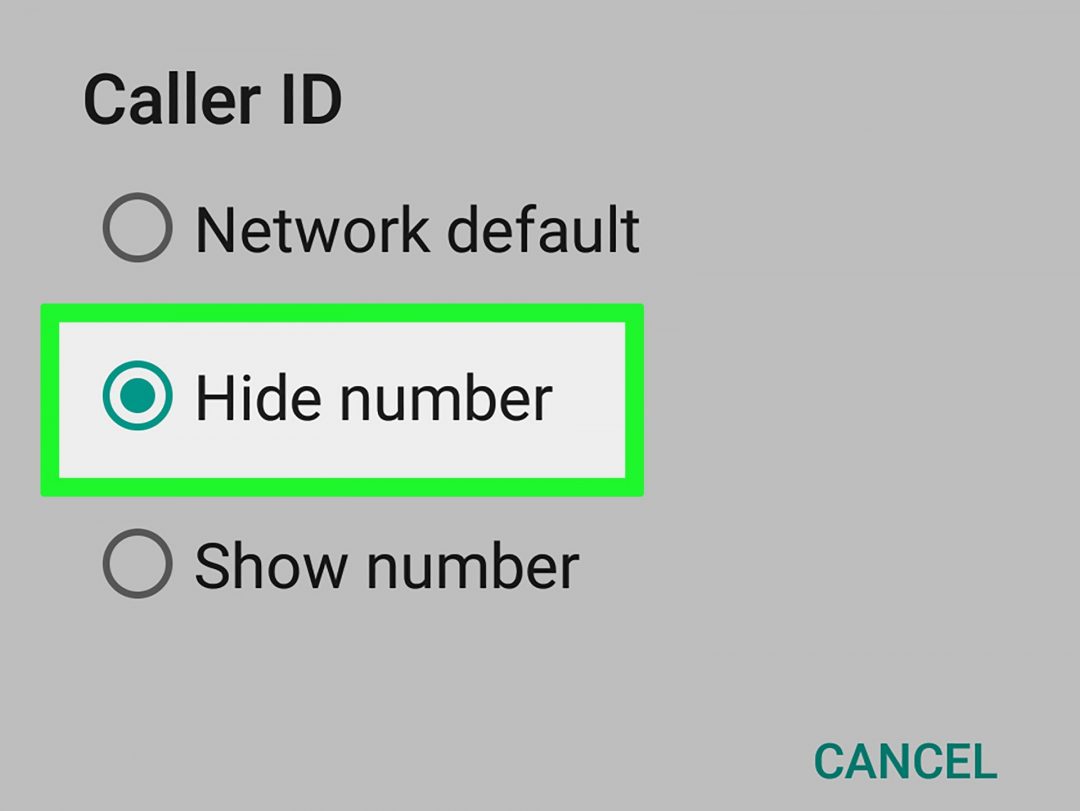
One of the most obvious ways to ensure your security when you have no option other than to use SMS based 2fa is to use a private, or very restricted phone number. This can be implemented a couple of different ways, but it’s important you take precautions and do it properly
How to implement 2fa on a private number
Firstly, you want to be careful about using virtual mobile numbers for 2fa. After all, the whole idea of virtual mobile numbers is that they’re connected to the internet and thus don’t function as a “second factor” of authentication most of the time. The exception to this is where you have some shared login (for example, to your domain registrar) that needs to be accessed by a bunch of different people. In that case, it can be useful to use a virtual mobile number to allow shared access to 2fa messages for multiple people, you just want to make sure that the way those people access those messages is protected by a more substantive form of 2fa using either an app, hardware token or private “real” mobile number (we do use BenkoPhone for this internally in some cases, and our messages all arrive via Trello for which we use Google with enforced 2fa as our SSO provider).
A better idea is to have a virtual mobile number as your public facing, business mobile number, and then have a very private “truly personal” mobile number that only close friends and family know, and use that as your 2fa number.
For folks in the USA/Canada, this is easy to do. Most business owners have a fully virtual mobile number through Google Voice or a similar provider that they can use from an app on their phone or through a web interface. This number can be published publicly, with the number on their SIM card being kept completely private from staff, clients and/or would be SIM jackers!!
There hasn’t really been a good option for the rest of us up until now. When we launched BenkoPhone, we made it possible to have a public facing business mobile number that works just like Google Voice, but for Australians (coming soon to Europe, the UK, South America and others!)
You can port your existing mobile number that everyone has (staff, clients, friends, family) into BenkoPhone and get a new, truly personal mobile number on a SIM card in your phone. Give that truly personal number to your close friends and family, and update any high risk 2fa configuration to use that much more private number.
That way, attackers can’t simply look your mobile number up on your website or in your email signature, find out your date of birth and get your number transferred to a new SIM card. Best of all, you can easily roll the same solution out for your staff. Anyone on your team who has their mobile number available on the website or in their email signature can use their personal number for setting up 2fa on any systems they have access to at your business. This dramatically reduces the attack surface area for hackers trying to socially engineer access to your organisation.
Get in touch with us today if you’d like to use BenkoPhone to step up your security game by using a “truly personal” mobile number for 2fa and regain more control over who contacts you, and when!